Managed IT vs. In-House IT: What Actually Works for Multi-Location Businesses? →
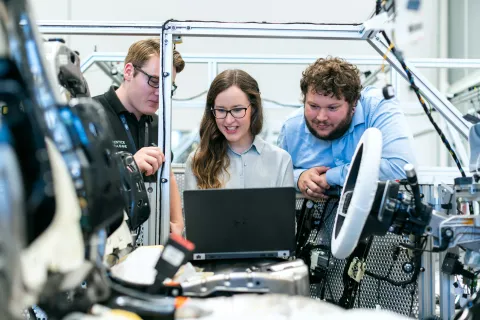
Why Your Manufacturing ERP Needs Better IT Infrastructure Your manufacturing ERP system is only as strong as the IT infrastructure supporting it. Even the best ERP software can slow production, corrupt order data,...

Imagine arriving at a home and finding the spare key tucked beneath the doormat. It's simple, convenient, and the first place anyone with bad intentions would check. That is exactly how many businesses handle...

Imagine it's Monday morning. You're fueled with coffee and equipped with a solid plan. This week is the one where you finally gain the upper hand. You step inside your office. But before you even set down your...

Remember the old days of blowing into Nintendo cartridges just to get them working? That was the original version of IT support. Cartridge not loading? Blow on it gently. Still nothing? Blow harder. If that didn't...

Springtime cleaning often starts with sorting through closets, but for many companies, the real mess isn't on a shelf or rack. It might be tangled in a server rack, hidden away in a storage closet, stacked in a back...

March 23, 2026 — ComTech is proud to announce that we are now part of Harbor IT. Harbor IT is a cyber-first managed services provider delivering integrated IT, cybersecurity, and cloud solutions for...
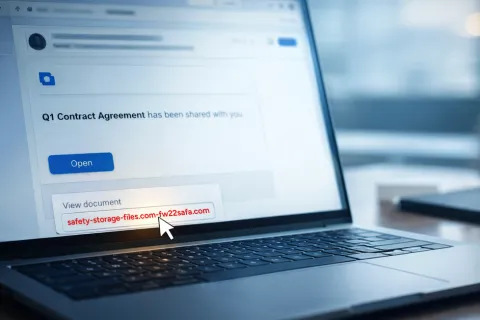
April 1 may pass with its usual pranks and false alerts, but the real threat lingers far beyond April Fools' Day. Sadly, scammers don't take a day off. Springtime marks a peak period for cybercriminals—not...

Managed IT vs In-House IT: What Works Best for Multi-Location Organizations Across North Carolina? As businesses across North Carolina continue to grow—expanding into new offices in Charlotte, Raleigh,...
It's Monday morning. Coffee ready. Laptop open. You're set to conquer the day. Then, a sudden nudge from your elbow sends the coffee flying. Time seemingly slows as the liquid spreads across your keyboard, seeping...

The Role of Managed IT Services in Supporting Multi-Location Businesses Across North Carolina Managing multiple business locations across North Carolina comes with operational complexity that many growing...

March marks the peak of tax season chaos. Your accountant is overwhelmed, your bookkeeper is racing against time, deadlines are closing in, and your inbox is flooded with urgent emails. Everyone is focused on just...

Key Challenges Faced by Multi-Location Businesses in North Carolina — And How Managed IT Services Help Growth brings opportunity. It also introduces operational strain — especially for multi-location...